In April 2019, I took the Offensive Security Wireless Attacks (WiFu) course and the OSWP exam. (Along with PenTest+ and Microsoft 365 Fundamentials, this was my third exam in a month!)
In brief, I enjoyed this. I thought the content was interesting, and the exam was actually fun (similar to an escape room). However, the course material was written in 2014 and it could do with an overhaul; Offensive Security updated the OSCP in Feb 2020, so hopefully they will do the same for the OSWP at some point.
In particular, the course objectives include these:
- The student will learn to implement attacks against WEP encrypted networks.
- The student will learn to implement attacks against WPA encrypted networks.
- The student will learn alternate WEP and WPA cracking techniques.
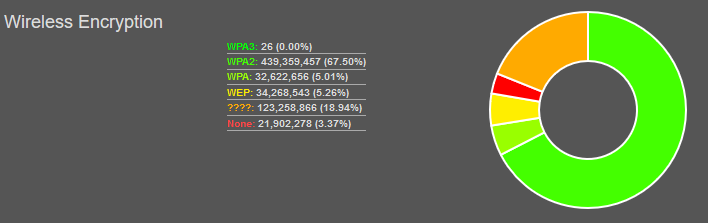
So, is this course/certification still relevant? How many people are actually using WEP/WPA rather than WPA2 (or open networks that don’t need cracking)? WiGLE (Wireless Geographic Logging Engine) has some stats on this. Here’s a snapshot from 2020-06-07:
In particular:
- 5.26% on WEP
- 5.01% on WPA
So, that’s about 10% of wireless networks. Based on that, I can see the skills being useful. However, when I scanned my local (residential) neighbourhood, I couldn’t find any WEP/WPA networks. Any new router from an ISP should come pre-configured with WPA2, and it’s been that way for several years now. I also wonder how up to date those stats are, i.e. whether the WEP networks still exist.
The good news (as a pen tester) is that the same attacks will work on WPA-PSK and WPA2-PSK. According to WiGLE’s stats, 67.5% of networks use WPA2, although unfortunately they don’t show a breakdown of Personal vs. Enterprise. If you’re using WPA2-Enterprise (802.1X authentication) then you’re safe against these attacks. However, in my anecdotal experience there are a lot of WPA2-PSK networks out there.
So, that’s a roundabout way of saying that yes, this exam is still relevant.
If you run a wireless network (at home or at work), how worried should you be? Before I did this course, I’d already heard that WEP is essentially worthless; now that I’ve experienced this from the attacker’s perspective, I can confirm that’s true. WPA2-PSK can be cracked, but it relies on a dictionary attack; if you’ve got a random passphrase then you’re pretty safe, e.g.
~*TJ8H|^u@<)Fk05Uq}t;5?N\v(bv<4s-nT`H””yA$(ha.bEP”+jEg)”&y({Fr
Continue reading “Offensive Security Wireless Professional (OSWP)”